Microsoft released a patch for the Exchange 2013/2016/2019 FIP-FS Scan Engine that has broken most on-prem Exchange servers as of this past midnight on 1/1/2022.
This custom backdoor lets attackers remotely steal tokens and certificates from Microsoft's identity platform.
A complete exploit for the remote code execution vulnerability in VMware vCenter tracked as CVE-2021-22005 is now widely available, and threat actors are taking advantage of it.
Apple released a critical software patch to fix a security vulnerability that researchers said could allow hackers to directly infect iPhones and other Apple devices without any user action.
Virtualization has been topping the list of buzzwords in 2021. It's a method that allows you to run multiple operating systems on one physical machine to keep your hardware costs down.
When it comes to use of social engineering in malware, the SirCam worm must be among the most insidious. The worm propagated itself in the usual way via email attachment. But SirCam didn’t carry a new email attachment—the typical “invoice” or “delivery confirmation” PDF.
Businesses that have been fortifying their computers against ransomware and other threats could be overlooking additional vulnerabilities within their ecosystem. IoT could be at risk.
What is a vulnerability? A system vulnerability is a flaw in the design of an operating system, application, or device that can be exploited by malicious entities to gain access and control of your system
Zero-day vulnerabilities in popular remote monitoring and management software targeted by threat actors to distribute ransomware to reportedly over one million systems.
Hackers Exploit Fortinet Flaw - Industrial enterprises in Europe are target of campaign, which forced a shutdown of industrial processes in at least one of its victims’ networks, according to researchers.
The company patched a vulnerability that could connected video and audio calls without the knowledge of the person receiving them.
SmarterMSP has highlighted the recent danger of malware and ransomware coming into email boxes tied to news of the day. An example might be an email appeal for funds related to post-election legal action or rebuilding after California’s wildfires.
Yet another software update fail has been unleashed by Microsoft, and this time it appears that the updates have ended up breaking Outlook with 0xc0000005 error
Is Apple really going to stop including the power adapter in-box for your brand new iPhone?
Twitter has issued an apology to its business clients acknowledging that personal information may have been compromised
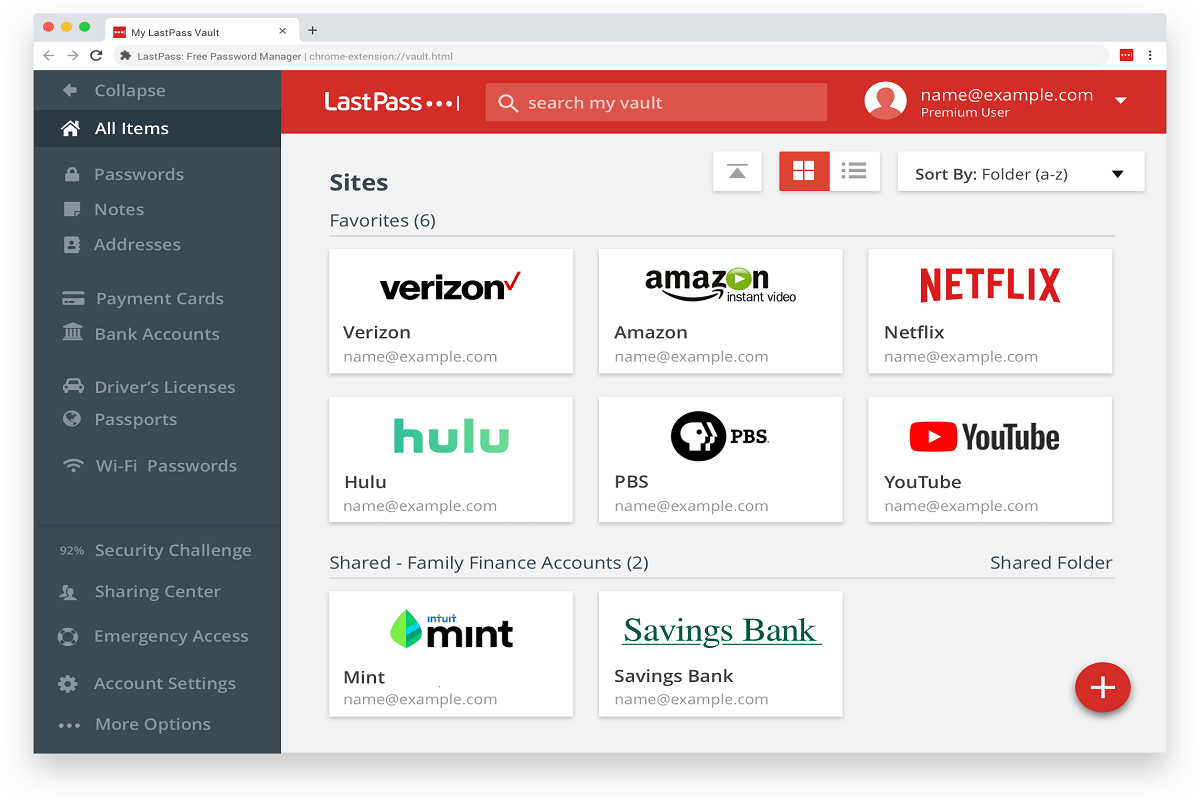
Passwords have been a staple for account identity verification for years, but with passwords continually reused or becoming easier to guess, users are realizing how vulnerable the tactic can be.
The war between data defenders and data thieves has been described as a cat-and-mouse game. How can the playing field be tilted in favor of the info-sec warriors? Here are five emerging security technologies that may be able to do that.